
How To Secure Your Business Website?
Why you should be concerned about your website security?
As one of the crucial communication channels with your customers, it is essential that your website presents a trustworthy image to viewers.
Imagine if someone were to browse your site, only to see notifications and indicators that your website is risky, they’d flee from your site for fear of their own privacy and safety.
 Imagine this warning sign appear on your website! Would anyone even dare browse your site?
In fact, you might even find yourself blacklisted by the search engines like Google, which greatly affects the traffic to your website, reducing the number of prospective customers.
It matters not whether you are a multinational corporation, or even a small home grown business. More often than not, hackers do not target a business specifically, but instead do a general scan to find websites that suffer from common vulnerabilities, making these easy targets to infiltrate.
As long as you run a website, you are a possible target for hackers, thus website security is something that everyone should be mindful of.
Imagine this warning sign appear on your website! Would anyone even dare browse your site?
In fact, you might even find yourself blacklisted by the search engines like Google, which greatly affects the traffic to your website, reducing the number of prospective customers.
It matters not whether you are a multinational corporation, or even a small home grown business. More often than not, hackers do not target a business specifically, but instead do a general scan to find websites that suffer from common vulnerabilities, making these easy targets to infiltrate.
As long as you run a website, you are a possible target for hackers, thus website security is something that everyone should be mindful of.

Simply put, HTTPS includes another layer of protection through SSL/TLS.
In regular HTTP, whatever users send through your website – be it sensitive data like passwords and credit card information, are easily accessible by outside parties in transit to your servers. Hackers who hack into any wifi (be it public or your home) would be able to access all these information from any HTTP sites you log into.
Simply put, HTTPS includes another layer of protection through SSL/TLS.
In regular HTTP, whatever users send through your website – be it sensitive data like passwords and credit card information, are easily accessible by outside parties in transit to your servers. Hackers who hack into any wifi (be it public or your home) would be able to access all these information from any HTTP sites you log into.

However, this tool is accessible to everyone, and as a business owner, you’ll want to be careful that bad players cannot make use of it. There are a few indicators you can take note of, and knowing some basic coding knowledge can help you better identify issues:
However, this tool is accessible to everyone, and as a business owner, you’ll want to be careful that bad players cannot make use of it. There are a few indicators you can take note of, and knowing some basic coding knowledge can help you better identify issues:



 For more extensive reading: https://danielmiessler.com/blog/how-to-explain-sql-injection-to-anyone/
For more extensive reading: https://danielmiessler.com/blog/how-to-explain-sql-injection-to-anyone/
 Always Backup Your Files
Backing up everything is one sure way to help you restore things back to order. The hackers may tamper with your database, lock your files or delete information from your system; but so long you have a backup, you can still minimise the damages and restore things back to a certain order.
All remember to setup an automatic backup system.
Always Backup Your Files
Backing up everything is one sure way to help you restore things back to order. The hackers may tamper with your database, lock your files or delete information from your system; but so long you have a backup, you can still minimise the damages and restore things back to a certain order.
All remember to setup an automatic backup system.
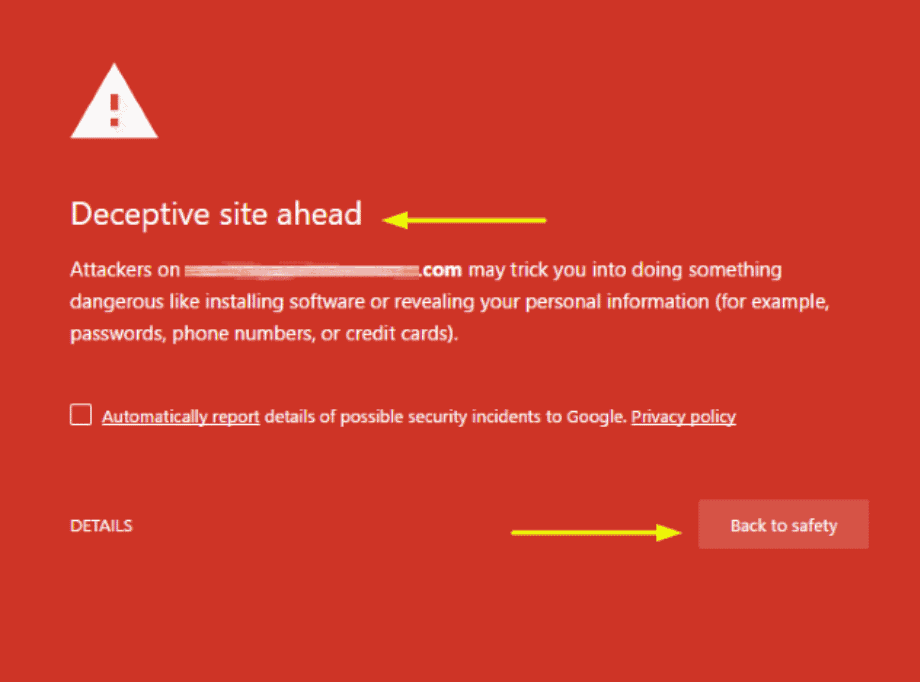 Imagine this warning sign appear on your website! Would anyone even dare browse your site?
In fact, you might even find yourself blacklisted by the search engines like Google, which greatly affects the traffic to your website, reducing the number of prospective customers.
It matters not whether you are a multinational corporation, or even a small home grown business. More often than not, hackers do not target a business specifically, but instead do a general scan to find websites that suffer from common vulnerabilities, making these easy targets to infiltrate.
As long as you run a website, you are a possible target for hackers, thus website security is something that everyone should be mindful of.
Imagine this warning sign appear on your website! Would anyone even dare browse your site?
In fact, you might even find yourself blacklisted by the search engines like Google, which greatly affects the traffic to your website, reducing the number of prospective customers.
It matters not whether you are a multinational corporation, or even a small home grown business. More often than not, hackers do not target a business specifically, but instead do a general scan to find websites that suffer from common vulnerabilities, making these easy targets to infiltrate.
As long as you run a website, you are a possible target for hackers, thus website security is something that everyone should be mindful of.
How to ensure your business is secure?
As a business owner, there are a variety of methods and platforms your website could have been built with. Some provide greater ease of set up, but at the cost of security and control; and vice versa. Depending on the approach used as well as your own exposure to code and web development, you could have different avenues to verify the security of your website. Here are some possible methods:HTTPS instead of HTTP
In this day and age, it’s fairly common for users to pay attention to simple indicators on whether a website is secure, and that should be your first consideration as the business owner. One such common indicator is the lock symbol in your browser url, which is only shown if your website has been verified as secure. HTTPS is one of the key differentiating factors used to verify this, but what exactly is the S in HTTPS? And how does it differ from regular HTTP? 
Simply put, HTTPS includes another layer of protection through SSL/TLS.
In regular HTTP, whatever users send through your website – be it sensitive data like passwords and credit card information, are easily accessible by outside parties in transit to your servers. Hackers who hack into any wifi (be it public or your home) would be able to access all these information from any HTTP sites you log into.
Simply put, HTTPS includes another layer of protection through SSL/TLS.
In regular HTTP, whatever users send through your website – be it sensitive data like passwords and credit card information, are easily accessible by outside parties in transit to your servers. Hackers who hack into any wifi (be it public or your home) would be able to access all these information from any HTTP sites you log into.
How about HTTPS websites?
HTTPS encrypts the data sent, which makes it indecipherable to anyone but the intended recipient, i,e you, ensuring that your customers data is protected. If you’re tech savvy enough, you can even go a step beyond and apply to get an Extended Validation(EV) HTTPS Certificate, which not only ensures that the data sent is secured, but also that you are a valid and trustworthy entity to users, further engendering their trust in you. Do take note that while seeing HTTPS and the lock symbol is a good indicator, it is not absolute certainty, as there may be portions of the transition that are not encrypted. If you are privy to the website setup, it would be a good idea to make sure that SSL/TLS is applied to every part of transit.Utilise Site Look and Browser Toolbars
Browser toolbars are a powerful tool in development, allowing developers to easily detect errors and identifying misplaced graphical elements. The way to get there is right click > Inspect and the toolbar will appear to you.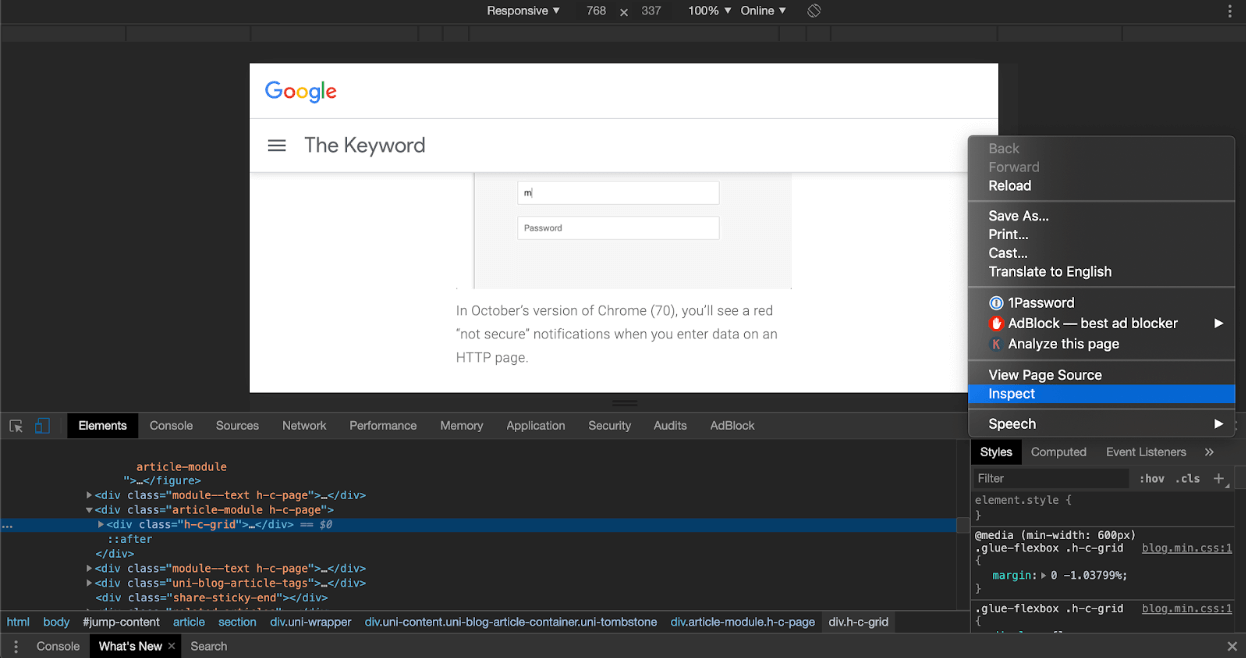
However, this tool is accessible to everyone, and as a business owner, you’ll want to be careful that bad players cannot make use of it. There are a few indicators you can take note of, and knowing some basic coding knowledge can help you better identify issues:
However, this tool is accessible to everyone, and as a business owner, you’ll want to be careful that bad players cannot make use of it. There are a few indicators you can take note of, and knowing some basic coding knowledge can help you better identify issues:
Console Messages
Console messages are a boon when it comes to fixing problems in your website, however, make sure to remove all of the messages that contain sensitive information or even errors when your site is accessible by the public. These messages can reveal information or give bad players insight to the working of your website, thereby opening it up to attacks.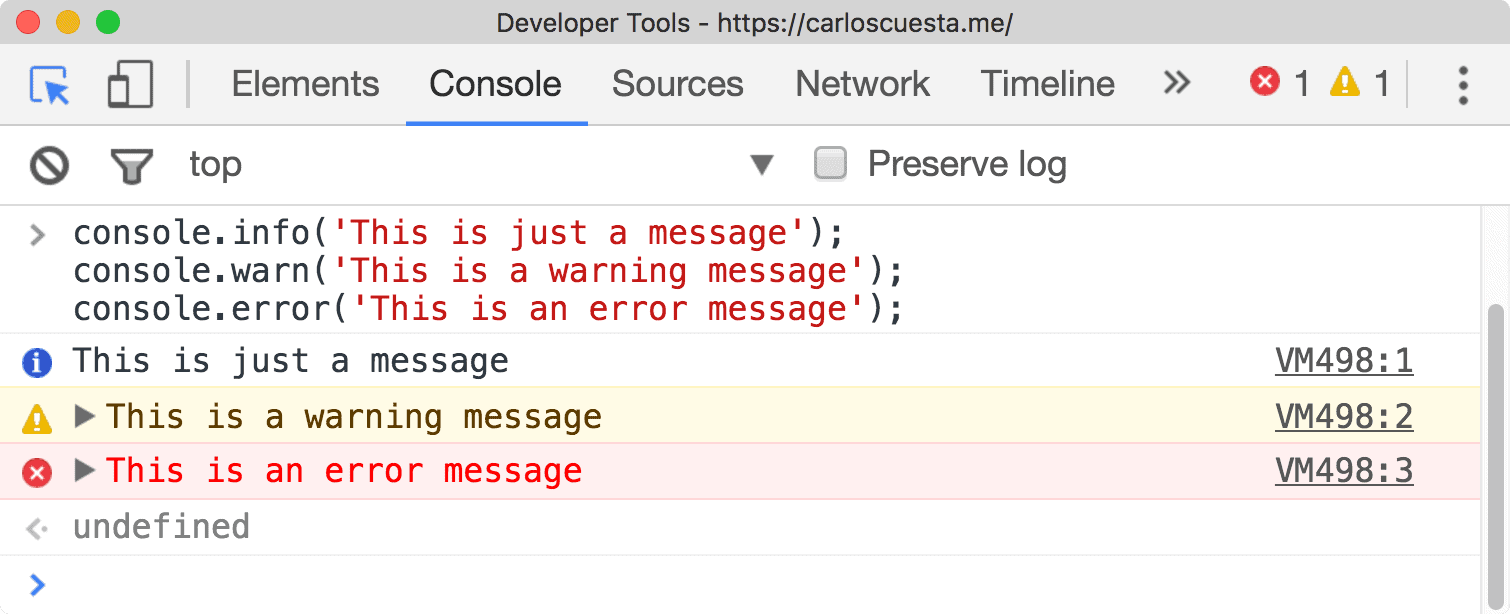
Defacement/ Hidden Elements
Another common indicator is if you discover that your website has been defaced, i.e unexpected pop ups or graphical elements that shouldn’t be on the website. Insidious actors may insert hidden elements into your website, which could affect your users or reduce your search engine ranking. Using your browser toolbar, it would be possible to navigate the elements that make up your page to identify suspicious elements.
Suspicious Network Activity
Using the browser toolbar, you can monitor any network requests that are made from your website. With a good understanding of what external resources are actually required by your website, you’ll be able to identify whether there are any suspicious requests that are being made from your website, which could be indicators that your website has been compromised.
Strong Passwords
It may sound like a no brainer with this but there are so many people who repeats the same mistakes every time. Strong passwords makes it harder for people to crack, and our advice is to not repeat the passwords if possible (check out services like 1password which allows you to have different password for all services without memorising them). Furthermore, if your website is a popular site that may have plenty of sensitive information, hackers are likely going to try to reuse information from third party data breaches to try to log into your business website. As a User
Nowadays most websites require users to sign up to access the website functions, and in this process, users need to provide passwords. As much of a hassle it is to enforce strong, secure passwords that use alphanumeric characters, this is crucial to ensure the security of your users accounts. In this day and age, simple passwords that only use text characters are far too easy to crack, thus it’s up to your website to help your users secure their accounts but preventing them from putting in passwords that are too easy. As an Administrator/ Owner
It’s fairly common to have an administrator interface to go with your website where you and your team could log into separately. It consists of a great deal of power and functions inaccessible to the normal user. If someone with harmful intentions get ahold of this account, it could seriously impair your business. Ensure that you do not use the default password and change it to a strong secure password as soon as possible. The more sensitive information you as a business hold, either for yourself or for your customers, the more you need to secure your administrator function. This includes:- Different levels of access to different levels of employees
- 2FA (Two-factor authentication) which requires you to put in a 6-digit code that is generated or sent to you, could be an added level of security for your staff
Update Your Software and Dependencies
Whether your website is built with a CMS tool like WordPress, or you hired a developer to build and deploy your website from scratch, there will always be software and dependencies that your website relies on to function. There is the potential for loopholes and vulnerabilities not just in your site, but these software and dependencies that were used to create your website. The producers of these items will periodically release updates and patches to fix these issues, and as the website owner, you’ll want to ensure that you are using the updated software and dependencies, to prevent bad players from exploiting old loopholes. If you are capable, you can also vet these external dependencies that are used in your website to ensure that you do not introduce vulnerable and exploitable points into your application. Other than your apps, you have to make sure your computers are well secured too (because you use computers to gain access to your apps, right?) Look into your own computer’s firewall and anti-virus software too. Make sure these software are updated as they are an added level of security on your own computer. SQL injection & Cross-Site Scripting(XSS)
Any area you accept input from users is a possible vulnerability in your application which you should check thoroughly, as you open up your app to users to access or store data. You’ll need to make sure that your website can handle unsafe input, as malicious actors may try to slip in code that could potentially disrupt your site, wreak havoc by revealing private information or destroy your entire database. Some of the common examples of this issue would be XSS and SQL injection. SQL Injection
- SQL injection means using special characters which would give a command to gain access to your database. Quite often, new apps today would already have features to prevent these but believe it or not, there are websites which are still vulnerable.
- Your database is where you store ALL your data points. Hackers write commands as inputs on forms available on your website, which when submitted, will execute on the database, and either allow them to steal information, or destroy the entire database.
- It might sound a little technical, but these are minimal requirements for your website.
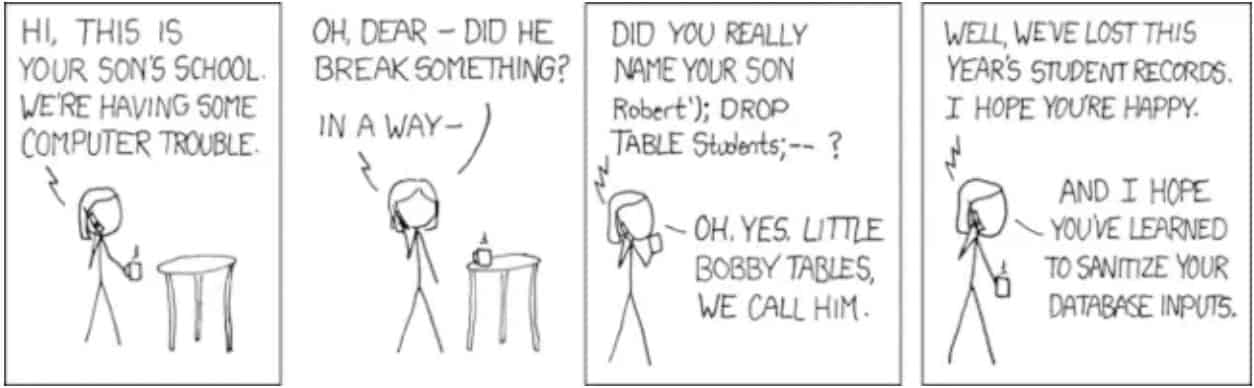 For more extensive reading: https://danielmiessler.com/blog/how-to-explain-sql-injection-to-anyone/
For more extensive reading: https://danielmiessler.com/blog/how-to-explain-sql-injection-to-anyone/
Cross-Site Scripting (XSS)
While XSS is similar to SQL injection in that it also involves keying in unsafe inputs that are executed, thereby compromising an entity, XSS differs in that it usually targets the users of the website, instead of the website itself. XSS attacks are typically used to redirect users to malicious websites or used to steal user credentials/information. For more extensive reading: https://www.cloudflare.com/learning/security/threats/cross-site-scripting/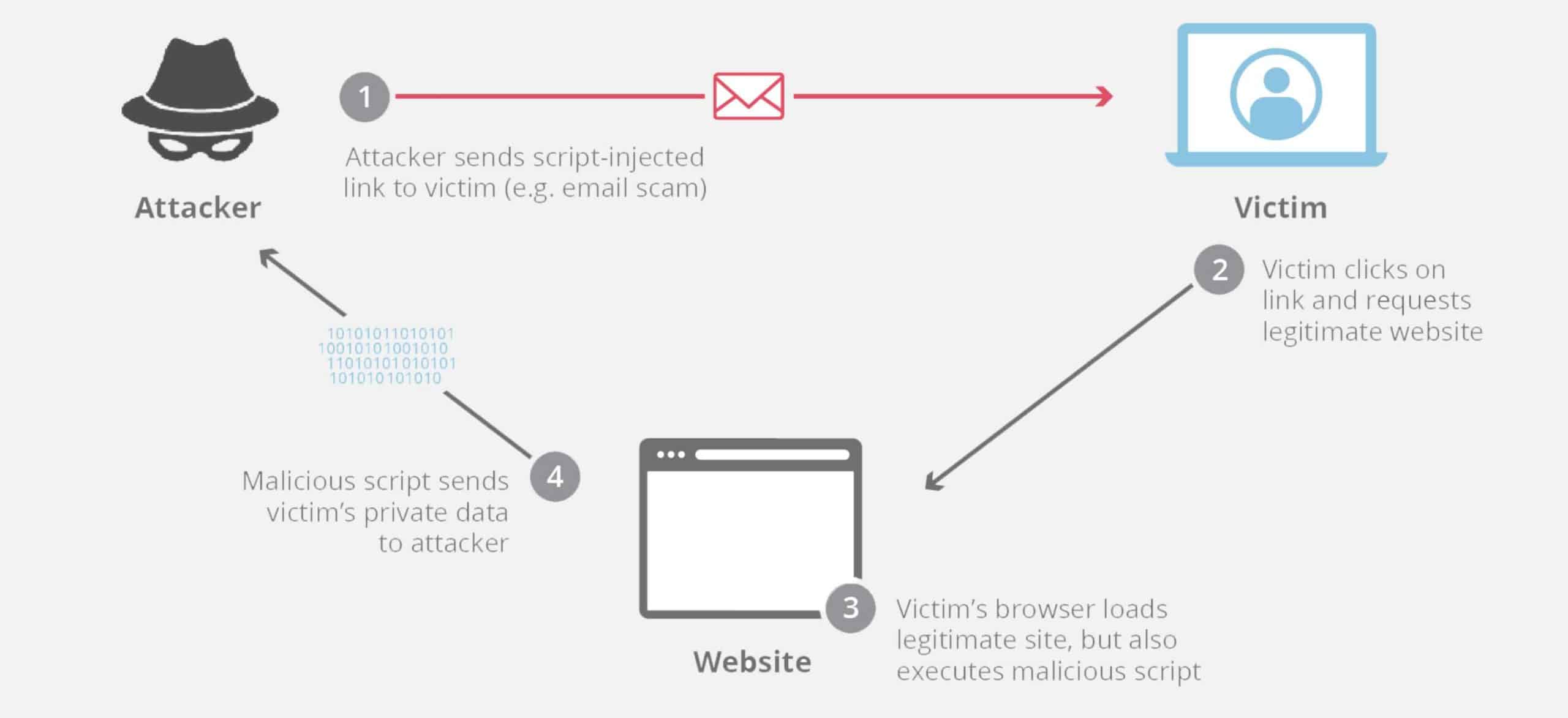 Always Backup Your Files
Backing up everything is one sure way to help you restore things back to order. The hackers may tamper with your database, lock your files or delete information from your system; but so long you have a backup, you can still minimise the damages and restore things back to a certain order.
All remember to setup an automatic backup system.
Always Backup Your Files
Backing up everything is one sure way to help you restore things back to order. The hackers may tamper with your database, lock your files or delete information from your system; but so long you have a backup, you can still minimise the damages and restore things back to a certain order.
All remember to setup an automatic backup system.
Education on Cybersecurity
Prevention is better than cure. Educating your team is important. You can setup and invest in security infrastructure for your business but many times, breaches are due to human errors and ignorance. Thus, educating your employees is most important on how to best protect themselves. When they protect themselves, they would be able to protect your business too. Hackers are getting more sophisticated. While you can imagine them to be geniuses who write code and break into stuff, believe it or not, a lot more of them are tricksters and they are there to trick you by leveraging on your negligence. For example, ransomware is one of the attacks where they would lock all your files and extort you for bitcoin to release the files. But how did the files get locked in the first place? Simple. It’s because the victim downloaded software from the internet thinking that it is secured, but in actual fact, it is a malicious software. The moment the victim opens the program, your computer is locked down. All these happened because of human ignorance and negligence. Here is an extensive list of ways hackers hack and how to protect yourself better. (link to main article) Conclusion
Don’t skimp out on security. Your website reflects on your business, and if you can’t protect yourself and your customers, you won’t be able to keep customers. No matter how big or small your business is, even if a breach will not reach the level of the Heartbleed event , or the case of Cambridge Analytica, there is no overstating the importance of website security. While knowing how to code is definitely a plus, non-coder business owners should still be aware of security vulnerabilities and take steps to rectify them, to ensure a safe and secure online experience for users. You can make use of online tools to generate reports on the security of your website, or hire services to do penetration testing on your website to test the security. But all in all, remember to education yourself and your staff!
4 Likes



